Shrinking federal IT budgets of the past few years have mandated the federal government to come up with new guidance and directives that outline steps to create plans that increase the overall efficiency of information technology. In the quest to “do more with less”, we now have a host of policies centered around topics such as cloud computing adoption, data center consolidation, program transparency, and shared services.
Although, it is predicted that cloud computing is going to see its highest level yet of government adoption this fiscal year, one shouldn’t ignore the continued call for shared services.
Shared services first
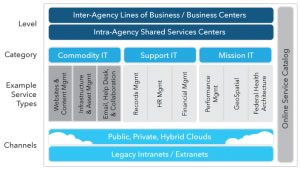
Shared services were designed to eliminate waste and duplication of IT assets. This agenda first surfaced in 2012 from the federal CIO in the form of the Federal IT Shared Services Strategy. In reality, cloud computing and shared services are very closely related. Creating a cloud environment, be it public, hybrid, or private, that offers automated, self-provisioned, and repeatable services, gives you the foundation to provide shared services across an organization.
One area in particular, that stands to benefit from a shared services strategy, is mobility. (You remember BYOD? It’s all we talked about right before cloud.) The government places mobility under the Commodity IT, category. The directive goes on to state that anything in the Commodity category is an immediate opportunity to build momentum in a shared services strategy. (See figure 1)
So, with this on the table for more than two years, why have not seen more shared service enterprise mobility infrastructures cropping up? And, I’m not talking about pilot programs. Two contributing factors that come to mind are mobile security, and organizational transformation. Both of these areas demand detailed attention.
Enter DISA’s DoD-wide mobile strategy
Moving into 2014, one large scale program in action that is worth watching, as it may set precedence for future large-scale secure mobile architectures, is the defense information systems agency (DISA) recent contract to develop and implement a DoD-wide mobile device management (MDM) and mobile application store (MAS). Slated for completion in mid-2014 (If all goes well) the program will have the capability to potentially support over 600,000 mobile devices. A DISA press release states that “The establishment of the MDM and MAS is the next major step forward in DOD’s process for building a multi-vendor environment, supporting a diverse selection of devices and operating systems.”
The need for mobility solutions
In order to make a project of this size successful, DISA needs to provide the same level of security on their mobile devices that currently exist on the desktop. Beyond that, an end-user experience must be created that is familiar to the user, and provides ease of use. Combining both of these effectively is not an easy task.
Multi factor authentication
For starters, a good multi-factor authentication verification solution must be established. This provides authentication based on what you know (password, PIN) with what you have (CAC, PIV card). A third element to consider that can be added is a biometric solution, such as a fingerprint reader or retina scanner. This type security is critical and backed by policies such as Homeland Security presidential directive 12 (HSPD-12), and OMB memorandum M-11-11.
Mobile device management
A good MDM solution allows you to gain visibility over any device connecting to your enterprise network, content and resources. You need to have the ability to rapidly enroll devices in your enterprise environment, and update device settings over the network to enforce security policies and compliance. For example, the DISA solution will have the ability to remove applications from an end device remotely.
End state, a perfect world
Eventually, as technology and security continue to progress, I envision a shared mobile environment that can 1.) Ensure mandatory security levels 2.) Present the user with a self-service catalog 3.) Offer an app store that develops can share and contribute code/API’s, and 4.) Is location transparent (think hybrid cloud).
The new federal shared services implementation guide identifies goals for federal IT teams as they move ahead, including improving return on investment and boosting productivity through use of innovative services and integrated governance processes. The CIO Council advises managers charged with implementing shared services of the importance of getting executive buy-in.
OMB is encouraging agencies not just to look at the shared service providers for human resources or financial management, but look at consolidating systems or contracts internally too. For example, using shared services, the Department of Commerce reduced the number of contracts to buy computers and is now paying 35% less for desktop computers and saving more than $200M on administrative costs. Several state and localities are also benefiting from the government to government shared services as described in the article here.